Project Overview
Vaultary is a comprehensive identity and security platform designed to help users analyze password strength, detect breaches, and manage credentials securely. It goes beyond simple rule-based checking by analyzing mathematical entropy and integrating with live breach databases.
1. Features
Vaultary is packed with features ensuring robust security and user management:
- Advanced Password Strength Analysis: Uses
zxcvbnto calculate entropy, crack time, and score (0-4). It provides specific feedback (warnings and suggestions) and visualizes the security breakdown using a Radar Chart. - Real-time Breach Detection: Integrates with the HaveIBeenPwned API to check if a password has appeared in known data breaches. It uses k-Anonymity (sending only the first 5 characters of the SHA-1 hash) to protect user privacy.
- Secure Password Vault: Allows users to save credentials (Site Name, URL, Username, Password). Passwords are encrypted using AES-256 Encryption (Fernet) before storage.
- User Authentication & Management: Supports local email/password login with Bcrypt hashing, OAuth (Google, GitHub, LinkedIn), email verification, and secure password resets.
- Two-Factor Authentication (2FA): Time-based One-Time Password (TOTP) support compatible with apps like Google Authenticator.
- Dashboard Tools: Includes profile management, an admin panel for user management, session timeout handling, and a secure server-side password generator.

2. Uses
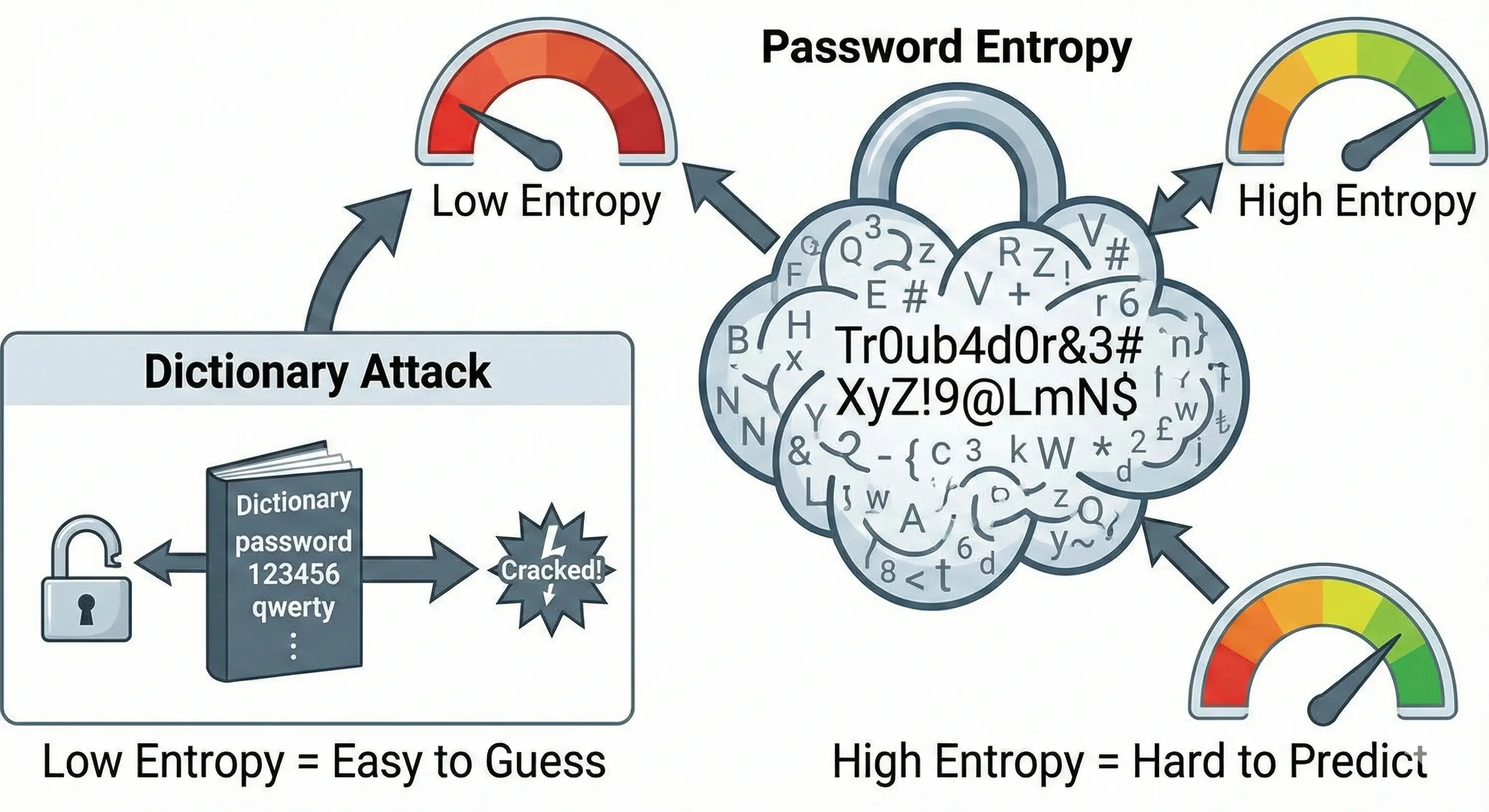
- Security Auditing: Users can test their passwords to see how long they would take to crack and if they are vulnerable to dictionary attacks or keyboard patterns.
- Credential Management: Acts as a web-based password manager to store login details securely.
- Identity Protection: Helps users verify if their credentials have been compromised in public leaks.
- Educational Tool: Demonstrates why certain passwords (like "P@ssword1") are weak despite meeting standard complexity rules.
3. The Vaultary Difference
Unlike traditional checkers that rely on simple rules (e.g., "1 uppercase, 1 number"), Vaultary offers:
- Entropy vs. Rules: Analyzes mathematical entropy (randomness) rather than just character counts.
- Pattern Recognition: Detects common patterns like keyboard walks (e.g., "qwerty"), repetitions, and common substitutions (e.g., '@' for 'a').
- Breach Integration: Connects to live breach databases to flag compromised passwords.
- Visual Analytics: Provides a graphical breakdown of why a password is strong or weak, rather than just a green/red bar.
4. Technical Stack
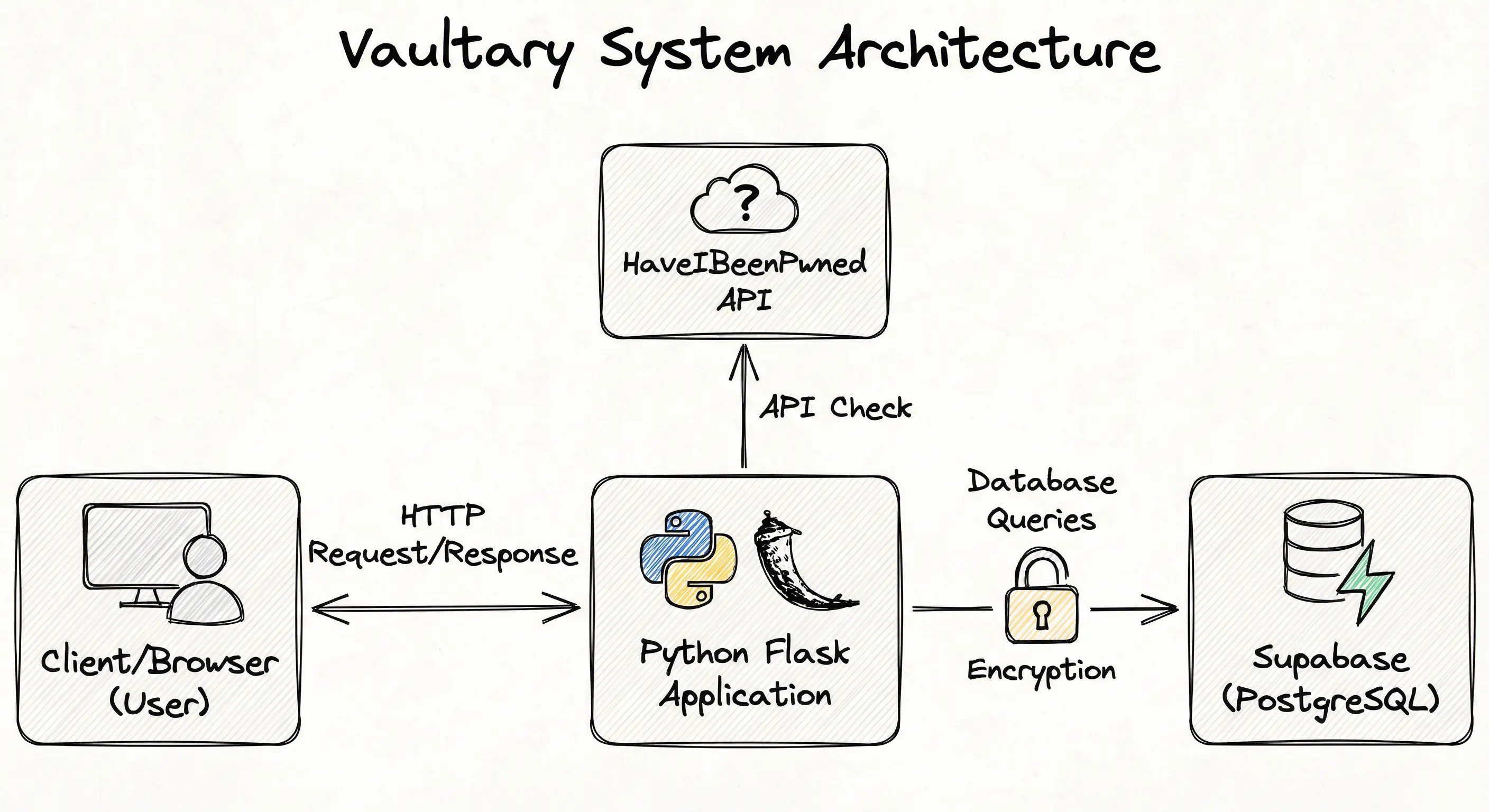
Backend Framework: Python Flask
Database: SQLAlchemy ORM (SQLite for dev, PostgreSQL for production)
Authentication: JWT (HTTP-only cookies), Authlib (OAuth), Flask-Bcrypt
Security Libraries: Cryptography (Fernet), Flask-Limiter, Flask-Talisman
Frontend: HTML5, CSS3 (Variables), Vanilla JavaScript, Chart.js
5. Code Review & Limitations
Based on the current codebase, here are some technical observations and areas for future improvement:
"Zero-Knowledge" Architecture
The current implementation claims "Zero-Knowledge," but the server holds the VAULT_KEY and performs decryption. In a true Zero-Knowledge architecture, decryption happens only on the client side using a key derived from the user's master password that the server never sees. Currently, if the server is compromised, the vault keys are accessible.
JWT Invalidation
The logout function simply clears the cookie on the client. Since JWTs are stateless, the token remains valid until it expires (1 hour). Implementing a token blacklist (e.g., using Redis) would prevent a stolen token from being used after logout.
Rate Limiting Storage
The limiter uses in-memory storage. If deployed on a platform with multiple workers (like Gunicorn) or serverless functions, rate limits might not be shared across instances, making them less effective.
Input Validation
While regex validation is present, adopting strict schema validation libraries (like Pydantic or Marshmallow) would enhance robustness against malformed data.
6. Future Roadmap
- Biometric Integration: Implementing WebAuthn for fingerprint login.
- Secure Notes: Extending the vault to store unstructured text data.